C is for Cybersecurity
Cybersecurity is NOT the same as information security.
Different words, different things.
What is “Cybersecurity”?
In order to fully appreciate the difference between information security and cybersecurity, we need to define both.
Information Security
The workable definition of information security that I’ve used for a decades is:
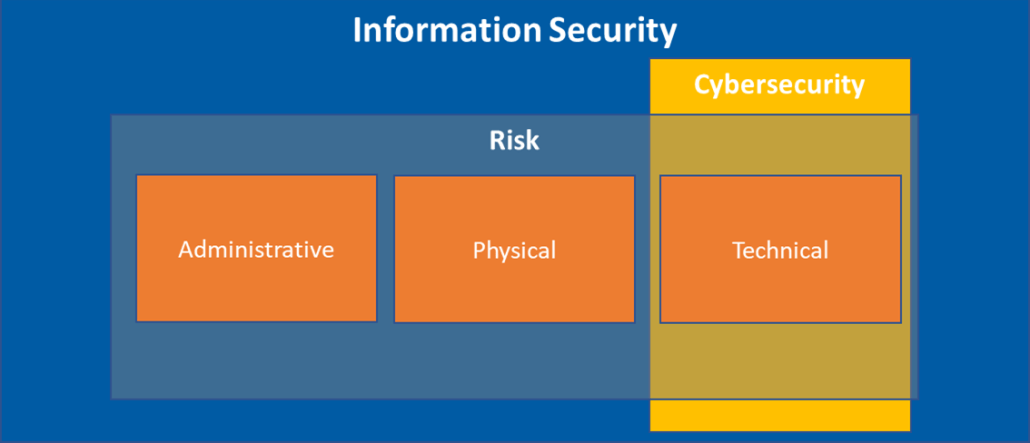
Managing risk to unauthorized disclosure, alteration, and destruction of information using administrative, physical and technical controls.
This is a workable definition because it hits all the necessary points:
- It’s “managing” risk, NOT eliminating risk. Eliminating risk is impossible.
- It’s a business issue, NOT an IT issue; therefore, administrative and physical controls cannot be dismissed. Two common phrases to drive this point:
- It’s easier to go through your secretary than your firewall.
- Nobody cares about your firewall when someone steals your server.
- Keeping things secret is important (confidentiality vs. disclosure), but so is making sure the information is accurate (integrity vs. alteration) and available (destruction).
OK. Now for “cybersecurity”.
Cybersecurity
Cybersecurity or “cyber security”, tomayto tomahto.
Seems this is a combination of two words, “cyber” and “security”. So then, what does “cyber” mean?
Let’s Google it:

Me being me, I’m not to be one who takes a single source of truth at face value, at least not if I can help it. What does Merriam-Webster say?

Alright good enough. Confirmed. Cybersecurity then is defined as:
Managing risk to unauthorized information disclosure, alteration, and destruction using technical controls.
Cybersecurity is a subset of information security. They are NOT the same. We could reason that cybersecurity and IT security are the same (or similar), but not cybersecurity and information security. Sort of looks like this:
If accuracy and language are important to us, which they should be, then we need get our words and terms straightened out.
Why This Matters
There are several reasons why it matters:
- There’s enough confusion already. Don’t believe me, go ask someone to define “cybersecurity” out of the blue. For the best results, ask three or four people who work in our industry and three or four people who don’t. Note three things:
- The bewilderment with the question.
- Their exertion in providing a clear answer.
- Differences between answers (yours and theirs, theirs and others, etc.).
- We’ve fought hard to make this a non-IT issue. The struggle is real. For 25+ years we’ve struggled to get business leaders to buy in and take responsibility for what’s theirs. We’ve been consistently preaching this isn’t an IT issue. We’ve trudged and plodded for slow progress. Now, we start using the word “cybersecurity” and we begin to lose ground. The ground we lose may seem insignificant, but ANY/ALL lost ground is bad. If you’ve fought this battle as long as some of us have, you know how hard we’ve grappled with this issue over the years.
- They’re both valid terms/words for what they’re already designed for. One word means one thing and one term means something different. They’re both perfectly valid for what they’re designed to communicate. Why mess?
How We Got Here
In my opinion, two reasons, marketing* and laziness.
Cybersecurity sounds cooler, sounds sexier, and probably sells more stuff (not necessarily stuff you/I need). Another reason might be laziness. Information security is eight syllables, and cybersecurity is six. We can save two whole syllables when using “cybersecurity! Think of all the cool things you could do with the extra syllables we’ve saved! I’ve even heard “experts” refer to information security as simply “cyber”. How sexy is “cyber”?! Using only two syllables?! Sounds super-experty too. The other six syllables can now be used to explain what you actually meant in the first place I guess.
Changing the meaning of words to fit marketing and/or laziness doesn’t seem right.
How To Get Back
Simple, use your words correctly. If you must use the word “cybersecurity”, preface it with what you’re actually talking about.
Honorable Mention for “C”
- Confidentiality – protecting from unauthorized disclosure or keeping information secret.
- Control – we can’t secure things we can’t control. A control is a restriction put upon an asset to protect it from unauthorized disclosure, alteration, and/or destruction. There are many applications of controls and control types, including access control, configuration control, change control, etc.
- Cryptography – the simplest meaning is “secret writing”. It’s turning plaintext data into encrypted data (ciphertext) and vice versa. Cryptography can be great for protecting against unauthorized disclosure and alteration of information, but doesn’t do anything for protecting against destruction.
Most people could have guessed what “C” was going to be. Next up is “D”.





